Information Security Alerts
Latest Alerts
Retirement Consultation Alert
CSU staff should be aware of the latest e-mail campaign being targeted at CSU employees. Employees have reported receiving e-mails from "aneasyretirement” or other related financial advisors who purport to be approved by the University, and which prompt you to sign up for an annual financial review.
The Alert:
While these vendors may be registered with the Financial Industry Regulatory Authority (FINRA), it is our understanding they are attempting to sell you services.
They have not been approved by the University nor have they been provided your contact information by the University.
An example of this e-mail includes the following (redacted in part)
Employee Doe,
Each year, as an employee of Columbus State University you are eligible to schedule a phone call, teleconference, or in-person meeting off campus with a representative for answers to your specific state, federal and individual retirement benefit questions.
At your consultation, you will be provided with information that will tell you what your potential income can be when you retire, and how much longer you may have to work. That, along with advice on the best ways to utilize your 401(a)/403(b) options with your state retirement and/or Social Security benefits.
Please be sure to indicate which type of appointment you prefer (off-campus, phone call, or teleconference) in the notes section while scheduling. Please also include your direct cell phone number.
Retirement Plans:
Employees under the age of 60 must participate in a basic retirement plan through the Teachers Retirement System of Georgia. Columbus State University requires all employees to participate in the state-mandated plans. The mandatory contribution is 6% of your pre-tax gross salary. Staff participate in the Teachers Retirement System of Georgia, but faculty and core administrators may choose Teachers Retirement System of Georgia or the Optional Retirement Plan.
We want you to be informed about the providers that are endorsed/approved by the University to assist you in funding a successful retirement future. Please refer to the following website for more information:
For information about the above, call the Human Resources Office at (706)507-8920
The APT group known as Silent Librarian has increased its spear phishing attacks as schools and universities are back.
The IT security researchers at Malwarebytes and Peter Kruse from the CSIS Security Group have reported on an Iranian APT (advanced persistent threat) group also known as Silent Librarian, TA407, and COBALT DICKENS that has been targeting schools and universities around the world with spear phishing attacks.
According to researchers, the malicious campaign has been up and running for the last couple of years however there has been a surge in attacks from the group as students and staff members of schools/universities are coming back after COVID-19 related lockdown.
It is worth noting that in March 2018, the US Department of Justice indicted nine Iranian citizens for targeting universities to steal sensitive research records. Since then the group has gone global and its activities continue to date.
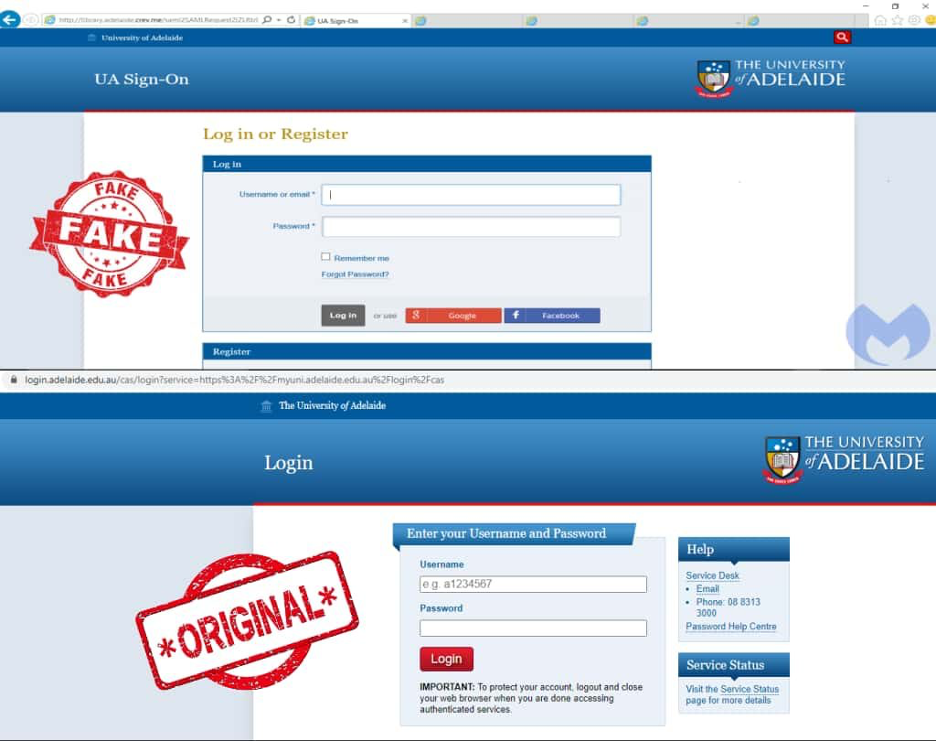
Silent Librarian operates by registering Top-level domains (TLD) with names similar to schools and colleges. A look at some of the sites operated by the group shows many of them had their login page cloned from original university sites to trick users into giving away their login credentials.
The group distributes messages that contain links or HTML attachments that direct victims to cloned university login portals. These portals incorporate stolen branding, accurate street addresses, and other social engineering techniques to manipulate users into disclosing login credentials.
Some of the university used in this attack include:
Fake and original University of Adelaide websites
In a blog post, Malwarebytes’ Threat Intelligence Team stated that although the group covers its tracks by using Cloudflare, the researchers were able to spot some of the sites powered by local hosting companies in Iran.
The researchers believe that this could be because of US sanctions on Iran which makes it nearly impossible to deal with companies in Europe, the US, or elsewhere.
It may seem odd for an attacker to use infrastructure in their own country, possibly pointing a finger at them. However, here it simply becomes another bulletproof hosting option based on the lack of cooperation between US or European law enforcement and local police in Iran, the company said.
Nevertheless, Iran based hackers have upped their game by continuously equipping themselves with tricks. In March last year, Microsoft had announced seizing 99 key websites that Iranian hackers used for stealing sensitive information from unsuspecting users in the US as well as launching cyberattacks.
In February 2020, researchers exposed the “Fox Kitten Campaign” in which an Iranian APT group was found hacking VPN servers to install backdoors to access networks of different organizations across the globe. Moreover, just last month, a six-year-long campaign called Rampant Kitten was exposed by researchers in which Iranian hackers were found utilizing Android backdoor apps.
Did you get an offer for student loan debt relief?
October 13, 2020
by, Traci Armani
Consumer Education Specialist, Division of Consumer & Business Education, FTC
Having trouble paying your student loan debt? You might get an offer that says you can reduce your monthly payment, or even reduce your overall debt. The offer might look like it comes from the government…and they might tell you that, first, you have to pay a fee. But it’s illegal for a company to ask you to pay a fee up front before they get you the promised relief. And it’s illegal for them to pretend to be from the government.
Because of the pandemic, people with federal student loans have some protections until December 31, 2020. People with student loans can also take steps to handle their student loan debt. Start by learning to spot the scams:
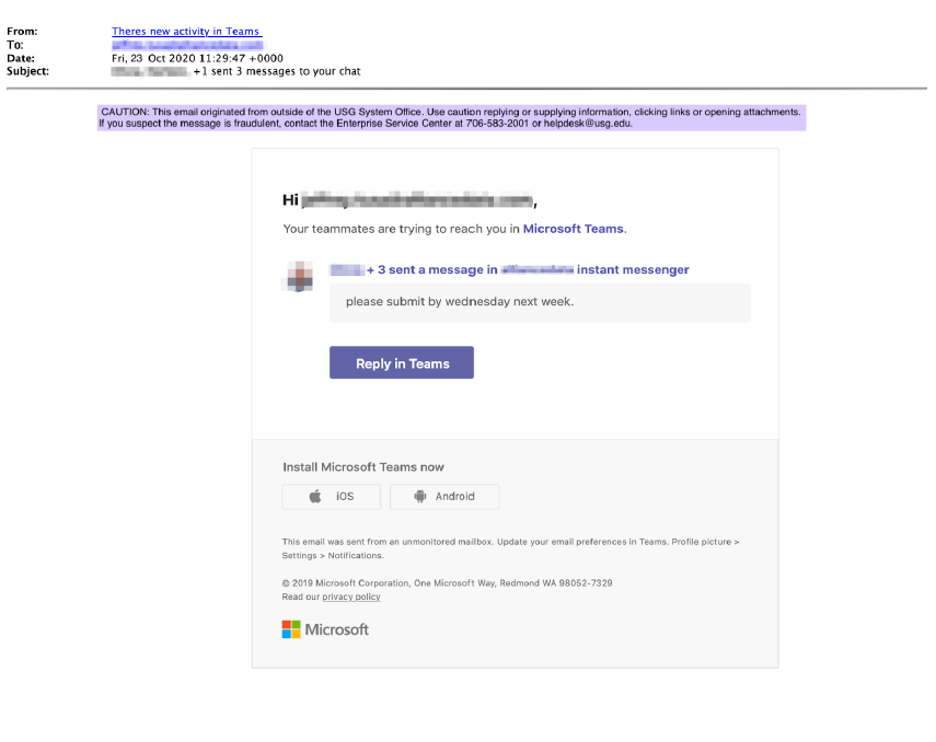
Researchers at Abnormal Security reported a new phishing campaign that impersonates automated messages and appears to originate from Microsoft Teams. The email currently displays the sender name, “There’s new activity in Teams.” The messages are very convincing and offer few obvious clues suggesting they are counterfeit. Below and attached are examples of a counterfeit message. Clicking on any link in the email will display a counterfeit Microsoft 365 login page to collect user names and passwords.
Rather than clicking on the Reply in Teams button or any other link in the email, USG Cybersecurity recommends users open the Teams application directly.